It sounds like an episode of ‘NCSI: S.W.A.T Five-0’ – and was probably once predicted by The Simpsons – but the recent cyber attack on Colonial Pipeline in the US could certainly have been foreseen by cyber experts and even just tech enthusiasts years ago.
The pipeline runs for 5,500 miles from Texas and Louisiana up America’s east coast to 14 states, including Virginia, New York and New Jersey.
It moves more than 2.5 million barrels of refined products such as gasoline, diesel and jet fuel daily.
The sheer number of valves and sensors on US oil refineries and pipelines have long made them an attractive target to cyber attackers, although this ransomware attack didn’t, on its own, cause the shutdown.
That was something the pipeline’s managers did in response to the attack, which was the admitted work of a criminal organisation known as DarkSide… believed to operate out of one of the former Soviet republics. For them, it’s all about the money and not intentionally “causing problems for society”.
The Colonial attack was probably helped by the coronavirus pandemic, with more engineers controlling systems for the pipeline from home using various kinds of remote access software.
However, although on the surface it appears to still be a clunky old system in places, Colonial does have a high-tech “smart pig” (Pipeline Inspection Gauge) robot that scurries through its pipes checking for anomalies and it’s more likely the hackers gained access to the company’s computer system through the administrative side of the business, where an employee may have been tricked into downloading some malware.
Internet of Things
Internet-connected technology, known as the Internet of Things (IoT), is now part of daily life – both personal and business – with smart assistants like Siri and Alexa to cars, watches, toasters, fridges, lights…and fish tanks!
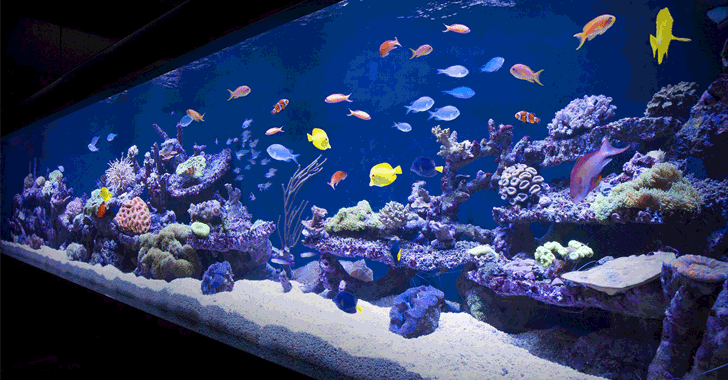
The story of the North American casino that was hacked through its internet-connected fish tank thermometer was one that certainly caught our attention a couple of years ago.
Hackers exploited a vulnerability in the thermostat of the magnificent aquarium in the casino’s lobby to get a foothold in the network. Once there, they managed to access the high-roller database of gamblers and then pulled it back across the network, out through the thermostat, and up to the cloud!
“It’ll never happen to us”
While the Colonial Pipeline issue may seem a long way removed from you and your (relatively) small business, perhaps the fish tank incident brings home the capabilities of some of these cyber criminals. Even if you don’t have millions in bank accounts to steal, think of the legal obligations you have to protect both the client and employee data held on your network, as well as any losses incurred if you’re unable to continue with business as usual for any length of time.
See more on our YouTube Channel here
With most electronic devices, the focus is on how well they perform with very little attention paid to how secure they are. Often their vulnerability, which can make them a weak link in the chain, isn’t even down to your neglect or lack of expertise in the cyber security field.
The manufacturers themselves often find out later what security flaws and loopholes are present in their devices and will issue a patch or update.
However, there are still measures you can take to protect yourself and your business in the meantime. And – you knew it was coming – this is where we come in:
Whether it’s Cyber Security, IT Consulting & Strategies, Cloud Services or Connectivity: Let us manage IT for you

